DOPPEL: Advanced DLL Proxying BOFs Now Available in IRIS C2
The red team landscape continues to evolve as defenders strengthen their detection capabilities around traditional techniques. Today, we're excited to announce the integration of the DOPPEL BOF Suite into IRIS C2 - a comprehensive collection of Beacon Object Files that transforms Matthew Eidelberg's groundbreaking FaceDancer research into production-ready, stealthy post-exploitation capabilities.
The Genesis: FaceDancer's Revolutionary Approach
In September 2024, Matthew Eidelberg (@Tyl0us) from Black Hills Information Security published groundbreaking research that fundamentally changed how we think about DLL hijacking attacks. Rather than relying on traditional search order hijacking or requiring elevated privileges, Eidelberg introduced the concept of DLL proxying - a technique that leverages misconfigured folder permissions and COM object manipulation to achieve code execution while maintaining application stability.
Eidelberg's research uncovered multiple zero-day vulnerabilities in Microsoft's ecosystem, including critical flaws in:
- Microsoft Teams Meeting Add-in (OneAuth.dll)
- Microsoft Edge's COM object loading
- New Outlook's registry-based DLL resolution
- Microsoft Teams v2's WindowsApps bypass techniques
What makes this research particularly significant is Microsoft's response - or rather, their lack thereof. Despite acknowledging these as valid zero-day vulnerabilities, Microsoft opted not to fix them, stating they don't meet their criteria for "DLL planting" issues. This decision effectively created a collection of forever-day vulnerabilities that remain exploitable across millions of enterprise endpoints.
From Proof-of-Concept to Production Arsenal
While Eidelberg's FaceDancer tool demonstrated the viability of these attacks, it remained primarily a research tool. Recognizing the immense potential for red team operations, we've transformed this research into the DOPPEL BOF Suite - five specialized Beacon Object Files that bring advanced DLL proxying capabilities directly into IRIS C2's post-exploitation framework.
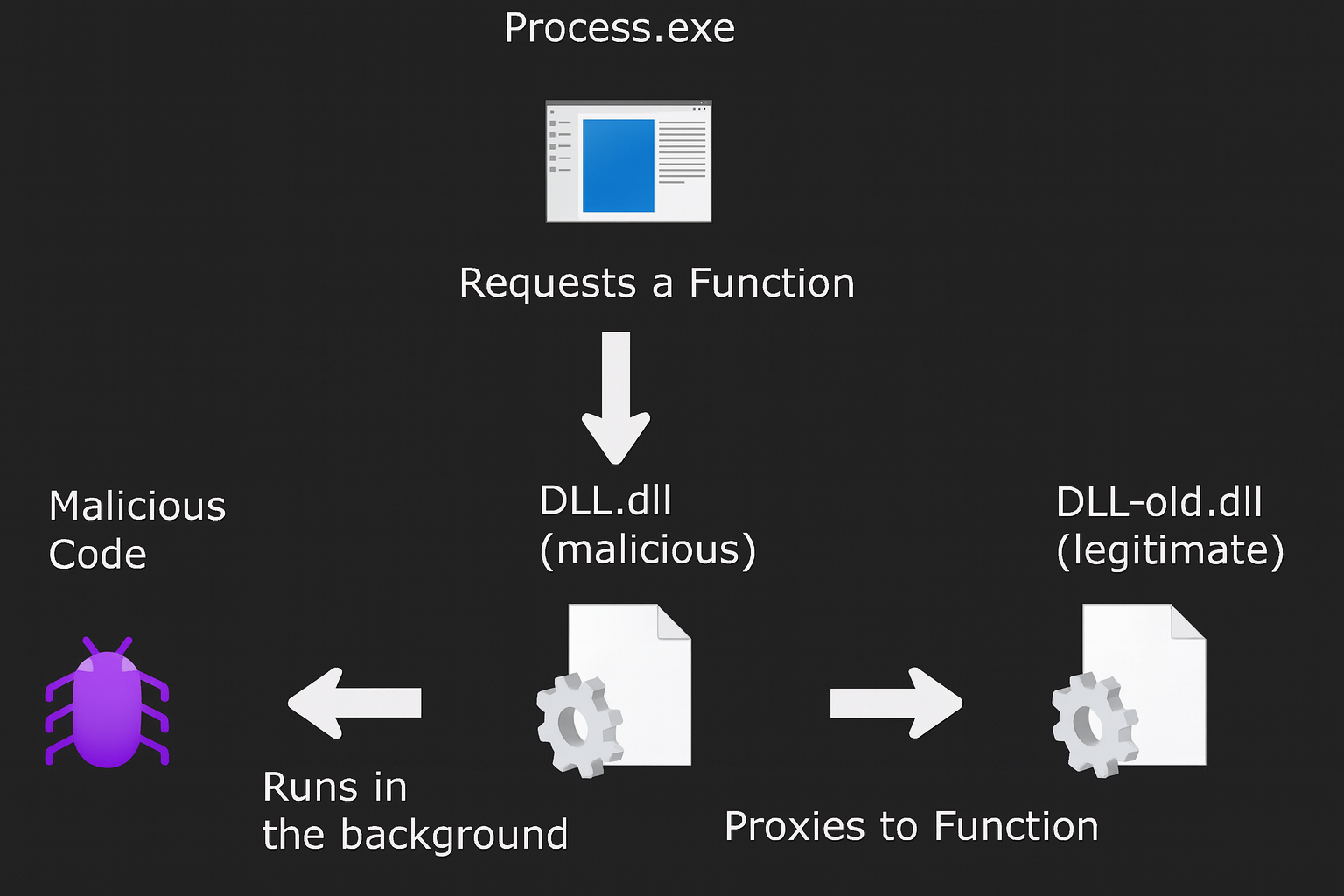
DLL Proxying Process: The malicious DLL intercepts function calls and proxies them to the legitimate DLL, maintaining application stability while executing malicious code.
The DOPPEL Architecture
DOPPEL (Dynamic Operations for Proxy-based Persistence and Evasive Loading) consists of five complementary BOFs, each designed for specific phases of the attack chain:
1. DOPPEL Analyze - Intelligence Gathering
// Core PE analysis functionality
typedef struct {
DWORD numberOfFunctions;
DWORD addressOfFunctions;
DWORD addressOfNames;
DWORD addressOfNameOrdinals;
} EXPORT_DIRECTORY_INFO;
// Enumerate exports for proxy generation
BOOL analyzeTargetDLL(LPCWSTR dllPath, BOOL generateDef);This BOF performs comprehensive PE analysis, extracting export tables and generating .def files necessary for function proxying. Unlike traditional tools that require disk-based artifacts, DOPPEL Analyze operates entirely in memory, parsing target DLLs and identifying exploitable function signatures.
2. DOPPEL Clone - Weaponized Proxy Generation
The crown jewel of the suite, DOPPEL Clone generates evasive proxy DLLs with four distinct sophistication levels:
- Level 0 (None): Direct execution with no evasion
- Level 1 (Basic): Domain membership checks and filename hashing
- Level 2 (Advanced): Sleep acceleration detection, hardware profiling, timing analysis
- Level 3 (Paranoid): Comprehensive sandbox detection, debugger evasion, process analysis
// Multi-layered evasion scoring system
int calculateEvasionScore(void) {
int score = 0;
if (!checkDomainMembership()) score += 2;
if (detectSleepAcceleration()) score += 3;
if (detectDebuggerPresence()) score += 4;
if (analyzeHardwareProfile()) score += 2;
return score;
}The generated proxy DLLs maintain full application functionality while executing embedded payloads, utilizing advanced techniques like API hashing, indirect calls, and staged memory allocation to evade detection.
3. DOPPEL Replace - Deployment and Persistence
Handles the operational aspects of DLL proxying attacks:
- COM registry key manipulation via HKCU\SOFTWARE\Classes\CLSID\
- File deployment with SHA-256 verification
- Automated backup and restoration capabilities
- Comprehensive cleanup for operational security
4. DOPPEL COM - Modern Application Targeting
Specifically designed to exploit Eidelberg's COM object research, this BOF targets:
- Microsoft Edge (msedge.exe) - Bypasses WindowsApps protection
- New Outlook (olk.exe) - Exploits registry-based DLL resolution
- Microsoft Teams v2 (ms-teams.exe) - Leverages COM hijacking vulnerabilities
The beauty of this approach lies in its simplicity - by creating registry entries in user-controlled HKCU locations, we can force these heavily protected applications to load our DLLs from arbitrary locations.
5. DOPPEL AppData - High-Value Targeting
Focuses on Eidelberg's most significant discovery - the OneAuth.dll vulnerability in Microsoft Teams Meeting Add-in. This BOF:
- Scans for vulnerable AppData installations
- Deploys proxy DLLs to user-writable directories
- Maintains automatic backup/restoration capabilities
- Targets the highest-value DLL in the modern enterprise stack
Technical Deep Dive: The OneAuth.dll Attack Vector
The OneAuth.dll attack represents the pinnacle of DLL proxying sophistication. When Microsoft Teams v2 integrates with Outlook, it installs the TeamsMeetingAddin package in a user-writable AppData directory:
C:\Users\[username]\AppData\Local\Microsoft\TeamsMeetingAddin\1.0\x64\OneAuth.dllThe attack sequence is elegantly simple:
- Reconnaissance: DOPPEL AppData scans for the OneAuth.dll installation
- Backup: Original DLL is renamed to OneAuth-legitimate.dll
- Deployment: Our proxy DLL is placed as OneAuth.dll
- Execution: When Outlook launches Teams meeting functionality, our DLL executes
- Proxying: All legitimate function calls are forwarded to OneAuth-legitimate.dll
This maintains complete application functionality while providing persistent code execution in the Outlook process - a critical target in any enterprise environment.
Advanced Evasion Techniques
The DOPPEL suite incorporates cutting-edge evasion methodologies that go far beyond traditional DLL hijacking:
API Hashing and Indirect Calls
// Resolve APIs by hash to avoid static strings
FARPROC resolveAPIByHash(DWORD hash) {
// Implementation obfuscated for operational security
return GetProcAddressByHash(hash);
}Multi-Stage Memory Allocation
Rather than allocating RWX memory pages that trigger EDR alerts, DOPPEL uses staged allocation:
// Stage 1: Allocate as RW
LPVOID mem = VirtualAlloc(NULL, size, MEM_COMMIT | MEM_RESERVE, PAGE_READWRITE);
// Stage 2: Copy payload
memcpy(mem, encryptedPayload, size);
// Stage 3: Change to RX
VirtualProtect(mem, size, PAGE_EXECUTE_READ, &oldProtect);Comprehensive Sandbox Detection
The paranoid evasion level implements a sophisticated scoring system that evaluates:
- Hardware characteristics (CPU cores, RAM, disk space)
- Timing anomalies (sleep acceleration, execution speed)
- Process environment (debuggers, analysis tools, VM artifacts)
- Network configuration (domain membership, DNS resolution)
Operational Impact and Red Team Applications
The DOPPEL suite fundamentally changes the red team landscape by providing:
1. Privilege Escalation Without Elevation
Traditional DLL hijacking requires administrative privileges to write to protected directories. DOPPEL attacks operate entirely within user-controlled spaces, making them accessible from any compromised user account.
2. Application Allowlisting Bypass
By leveraging legitimate applications (Outlook, Edge, Teams) to load our DLLs, we completely bypass application allowlisting solutions. The host process is trusted, making detection significantly more challenging.
3. Persistent Code Execution
COM registry entries persist across reboots, providing a reliable persistence mechanism that doesn't rely on traditional startup locations monitored by security tools.
4. High-Value Process Injection
Gaining code execution within Outlook, Edge, or Teams processes provides access to:
- Email communications and contacts
- Browser sessions and stored credentials
- Corporate communications and file shares
- Single sign-on tokens and authentication artifacts
5. Evasion of Modern EDR
The combination of legitimate process hosting, user-space operations, and advanced evasion techniques makes these attacks particularly challenging for endpoint detection and response solutions to identify.
The Microsoft Response: A Security Community Perspective
Microsoft's decision not to address these vulnerabilities deserves particular attention. Despite Eidelberg's thorough disclosure process and clear demonstration of the security implications, Microsoft's responses were dismissive:
First Response (April 2024): "We've determined that this issue does not meet the bar for security servicing... we've marked your finding for future review as an opportunity to improve our products."
Second Response (August 2024): "Upon review this does not meet any of the categories of DLL planting issue that the MSRC services. For an attacker to leverage this to get code execution on a machine, they would have to already have code execution on the machine."
This response demonstrates a fundamental misunderstanding of red team operations and lateral movement techniques. The argument that "code execution is required for code execution" ignores the reality that initial access is often limited and privilege escalation, persistence, and process migration are critical phases of any sophisticated attack.
Microsoft's stance effectively creates a permanent attack surface across their entire ecosystem - a decision that significantly benefits red team operations while leaving defenders with limited recourse beyond detection-based controls.
Integration with IRIS C2
The DOPPEL BOFs integrate seamlessly into IRIS C2's post-exploitation framework, appearing as standard modules within the BOF category. Each module includes:
- Comprehensive parameter validation with suggested values
- MITRE ATT&CK technique mapping for proper categorization
- Detailed usage documentation with operational examples
- Built-in operational security features including cleanup capabilities
- Advanced logging for attack chain documentation
Example Operational Sequence
# Phase 1: Reconnaissance
usemodule bof/doppel/doppel-com
set Operation enumerate
execute
# Phase 2: Target Selection
usemodule bof/doppel/doppel-appdata
set Operation scan
set TargetDll OneAuth.dll
execute
# Phase 3: Deployment
set Operation deploy
set ProxyDllPath /path/to/payload.dll
execute
# Phase 4: Trigger (user launches Outlook meeting)
# Phase 5: Cleanup
set Operation cleanup
execute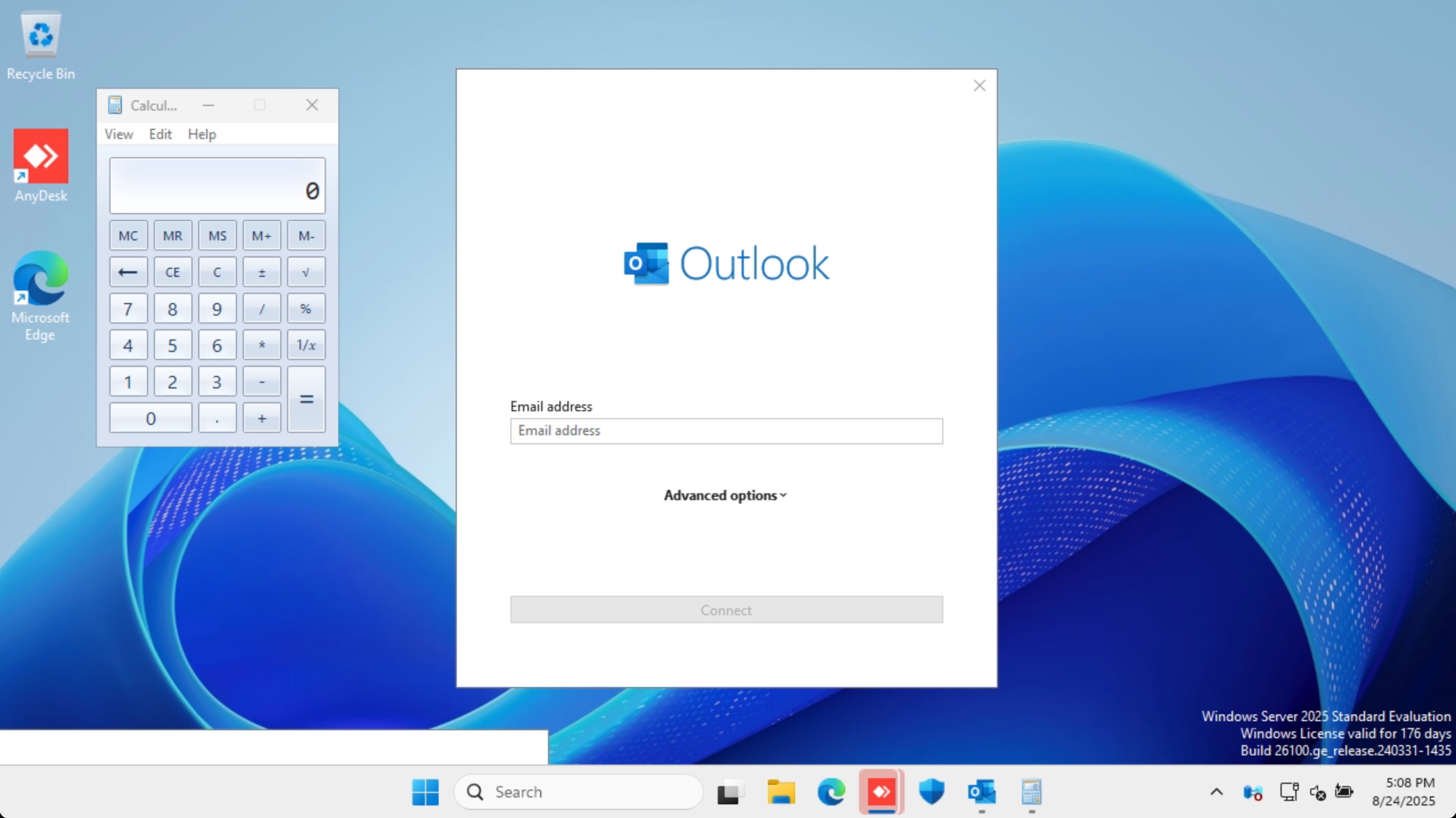
Attack Success: When Microsoft Outlook is launched, the DOPPEL proxy DLL successfully executes calc.exe while maintaining normal application functionality. This demonstrates the stealth and reliability of the DLL proxying technique.
The Future of DLL Proxying
The DOPPEL suite represents just the beginning of what's possible with advanced DLL proxying techniques. As Microsoft continues to harden traditional attack vectors, techniques that leverage legitimate application behavior and user-controlled resources become increasingly valuable.
The research foundation laid by Matthew Eidelberg has opened an entirely new category of attacks that combine the stealth of living-off-the-land techniques with the reliability of traditional DLL hijacking. By transforming this research into production-ready BOFs, we're providing red teams with capabilities that will remain relevant for years to come.
Conclusion
The integration of the DOPPEL BOF Suite into IRIS C2 represents a significant advancement in post-exploitation capabilities. By building upon Matthew Eidelberg's groundbreaking FaceDancer research, we've created a comprehensive toolkit that transforms forever-day vulnerabilities into reliable, stealthy attack vectors.
These BOFs don't just provide new techniques - they represent a fundamental shift in how we approach DLL-based attacks. By focusing on proxying rather than hijacking, leveraging user-controlled resources rather than requiring elevation, and maintaining application stability rather than causing disruption, DOPPEL attacks are perfectly suited for sophisticated red team operations in modern enterprise environments.
The fact that Microsoft has explicitly chosen not to address these vulnerabilities only strengthens their operational value. Unlike traditional exploits that may be patched, these techniques leverage fundamental architectural decisions in Windows and Microsoft's application ecosystem - decisions that are unlikely to change without significant re-engineering efforts.
For red teams seeking to enhance their post-exploitation capabilities with cutting-edge techniques that bypass modern security controls, the DOPPEL BOF Suite provides an unparalleled advantage in today's defensive landscape.
Ready to step up your red team operations? The DOPPEL BOF Suite is now available as part of IRIS C2's comprehensive post-exploitation framework. Learn more about IRIS C2's advanced capabilities and how they can enhance your security assessments by reaching out to info@IRISC2.com.
Special thanks to Matthew Eidelberg (@Tyl0us) and Black Hills Information Security for their groundbreaking research that made this development possible. The security community benefits immensely from researchers willing to push boundaries and challenge conventional thinking about attack methodologies.